Introduction
In today’s hyper-connected digital ecosystem, organizations no longer operate from a single centralized data center. Instead, data is continuously generated at the edge of the network — from IoT sensors, smart devices, mobile applications, industrial machines, and remote offices.
However, while edge computing improves speed and reduces latency, it also introduces a serious security challenge.
👉 The closer data moves toward users, the closer attackers get to sensitive information.
Therefore, traditional perimeter-based security models fail to protect modern distributed infrastructure. Businesses must now protect data at its origin, not after transmission.
This concept is called:
Edge Computing Security — securing devices, processing, and communication directly where data is generated.
According to modern cybersecurity frameworks similar to the protection strategies discussed in enterprise security platforms like BotDef, attacks increasingly target endpoints rather than centralized servers. Consequently, protecting the edge is no longer optional — it is mandatory.
🧠 What is Edge Computing?
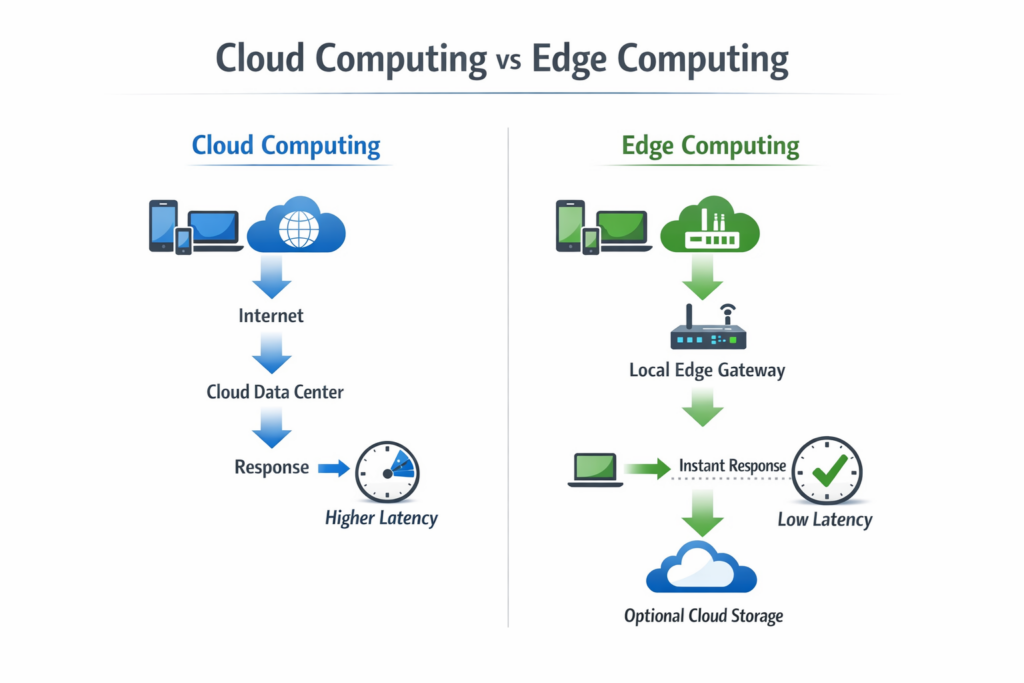
Edge computing is a distributed computing architecture where data processing occurs near the data source instead of sending everything to cloud servers.
Traditional Cloud Flow
Device → Internet → Cloud Server → Processing → Response
Edge Flow
Device → Local Edge Node → Processing → Response → (Optional Cloud Storage)
Because processing happens locally, performance improves dramatically.
However, security responsibility also shifts locally.
Why Edge Computing Creates New Security Risks
Although edge computing improves speed, it significantly expands the attack surface.
Key Risk Factors
- Thousands of endpoints
- Uncontrolled physical environments
- Weak device firmware
- Limited patch management
- Insecure network connections
- Real-time decision dependency
In centralized systems, you protect one data center.
In edge systems, you protect every device.
Therefore, attackers prefer edge networks because compromising one device may provide entry into the entire infrastructure.
⚠️ Common Edge Computing Attacks
1. Device Hijacking
Attackers gain control of IoT or endpoint devices.
Example:
Security cameras become botnet participants.
2. Man-in-the-Middle (MITM)
Data intercepted between device and processing node.
3. Firmware Injection
Malicious firmware replaces original software.
4. Data Poisoning
False sensor data manipulates AI decisions.
5. Distributed Denial of Service (DDoS)
Compromised edge devices launch coordinated attacks.
Modern threat intelligence systems — similar to network behavior detection approaches discussed in advanced security research — focus on identifying abnormal device activity patterns instead of relying only on signatures.
🛡️ Core Principles of Edge Computing Security
To protect distributed infrastructure, organizations must follow a layered defense model.
1. Zero Trust Architecture
Never trust. Always verify.
Each device must authenticate continuously.
Instead of trusting internal network traffic, verification happens for every request.
🔗 External Reference:
https://www.cloudflare.com/learning/security/glossary/what-is-zero-trust/
2. Strong Device Identity
Every device needs a unique cryptographic identity.
Methods:
- Hardware root of trust
- TPM chips
- Secure certificates
- Device attestation
Without identity verification, edge networks become anonymous networks — extremely dangerous.
3. End-to-End Encryption
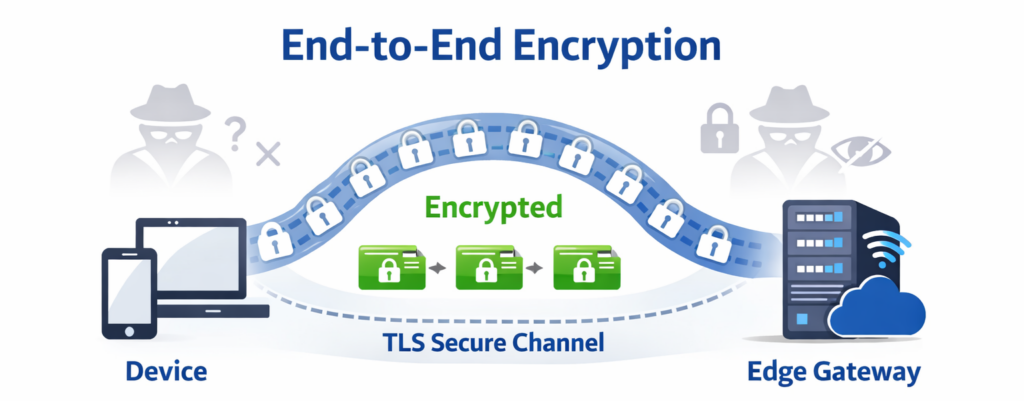
Data must be encrypted:
- At rest
- In transit
- During processing
Protocols:
- TLS 1.3
- DTLS
- Secure MQTT
- IPSec tunnels
Therefore, even if intercepted, the data remains unreadable.
4. Micro-Segmentation
Instead of one large network, divide infrastructure into secure zones.
Compromised devices cannot move laterally.
Example:
Factory robots separated from payment terminals.
5. AI-Based Threat Detection
Traditional antivirus fails because edge attacks are behavior-based.
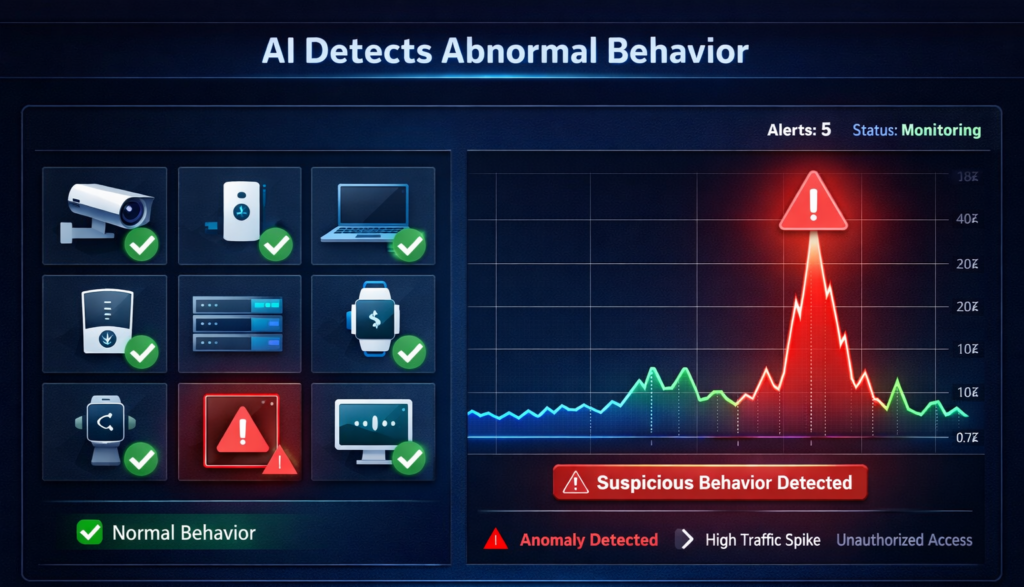
Modern protection monitors:
✔ abnormal device behavior
✔ unusual traffic spikes
✔ unauthorized commands
Security approaches similar to behavioral detection engines described in platforms such as BotDef focus on detecting intent rather than signature, which significantly improves detection of unknown attacks.
🧩 Edge Security Architecture Layers
Device Layer Security
Secure Boot
Device only runs trusted firmware.
Hardware Root of Trust
Physical chip validates operating system.
Firmware Integrity Monitoring
Prevents firmware replacement.
Network Layer Security
Secure Communication Protocols
Encrypted channels only.
Network Access Control
Unauthorized devices automatically blocked.
Traffic Inspection
Real-time packet analysis.
Application Layer Security
API Authentication
OAuth2 / JWT validation.
Container Security
Secure edge containers prevent malicious workloads.
Runtime Monitoring
Detect suspicious commands instantly.
🔄 Edge vs Cloud Security (Important Comparison)
| Feature | Cloud Security | Edge Security |
|---|---|---|
| Location | Centralized | Distributed |
| Attack Surface | Limited | Massive |
| Latency | Higher | Ultra-low |
| Monitoring | Easier | Complex |
| Required Protection | Network perimeter | Device identity |
Therefore, edge security must be proactive, not reactive.
🏭 Real-World Use Cases
Smart Cities
Traffic sensors must be secured or attackers can manipulate signals.
Healthcare Devices
Medical monitors must protect patient data locally.
Industrial Automation
Compromised robots can halt production lines.
Retail Analytics
Camera analytics must prevent customer data leakage.
🔐 Best Practices for Implementing Edge Computing Security
✔ Use Hardware-Backed Authentication
Prevents fake devices joining network.
✔ Implement Continuous Monitoring
Detect compromise immediately.
✔ Patch Devices Automatically
Outdated firmware causes most breaches.
✔ Apply Least Privilege Access
Devices access only required resources.
✔ Maintain Security Visibility
Central dashboard monitors distributed nodes.
📊 Future of Edge Security
Edge computing will integrate with:
- AI cybersecurity
- Autonomous response systems
- Self-healing networks
- Predictive threat intelligence
Eventually, security will shift from detection → prevention → prediction.
Conclusion
Edge computing transforms performance, automation, and real-time intelligence. However, it simultaneously transforms cybersecurity risk.
Organizations must understand:
Data is safest when protected where it is created — not where it is stored.
Therefore, combining device identity, zero trust, encryption, and behavioral monitoring ensures a resilient infrastructure capable of resisting modern cyber threats.
Businesses that secure the edge today will prevent breaches tomorrow.







