The Role of 5G in Cybersecurity – Faster, but Safer?
The role of 5G in cybersecurity is becoming one of the most critical discussions in modern technology. While 5G networks promise ultra-fast speeds, low latency, and massive connectivity, they also introduce new security challenges. Therefore, organizations must rethink their cybersecurity strategies to remain protected.
As businesses adopt 5G infrastructure, the question is no longer whether 5G is fast — it is whether 5G is secure enough.
⚡ “Speed without security is vulnerability in disguise.”
In this comprehensive guide, we explore how 5G transforms cybersecurity, what new risks emerge, and how advanced protection mechanisms — including AI-driven platforms like BotDef — help mitigate evolving threats.
What Makes 5G Different From Previous Generations?
Before analyzing the role of 5G in cybersecurity, it is important to understand what makes 5G fundamentally different.
Key Technical Features of 5G
1. Ultra-Low Latency
5G reduces latency to nearly 1 millisecond. As a result, real-time applications like autonomous vehicles and remote surgeries become possible.
2. Massive Device Connectivity
Unlike 4G, 5G supports millions of IoT devices per square kilometer. However, this also increases the number of potential attack points.
3. Network Slicing
5G introduces network slicing, allowing multiple virtual networks on the same infrastructure. While this enhances efficiency, it also creates segmentation risks.
4. Edge Computing Integration
Because data processing moves closer to the user, 5G reduces delay. Nevertheless, edge nodes may become vulnerable attack targets.
How 5G Impacts Cybersecurity Architecture
The role of 5G in cybersecurity extends beyond faster networks. It fundamentally changes how security frameworks must operate.
Expanded Attack Surface
With billions of IoT devices connected, attackers gain more entry points. Consequently, traditional perimeter-based security models become ineffective.
For example:
- Smart cities
- Connected factories
- Autonomous transportation
- Healthcare IoT systems
Each device represents a potential vulnerability.
According to the European Union Agency for Cybersecurity (ENISA), 5G supply chain complexity significantly increases systemic risk.
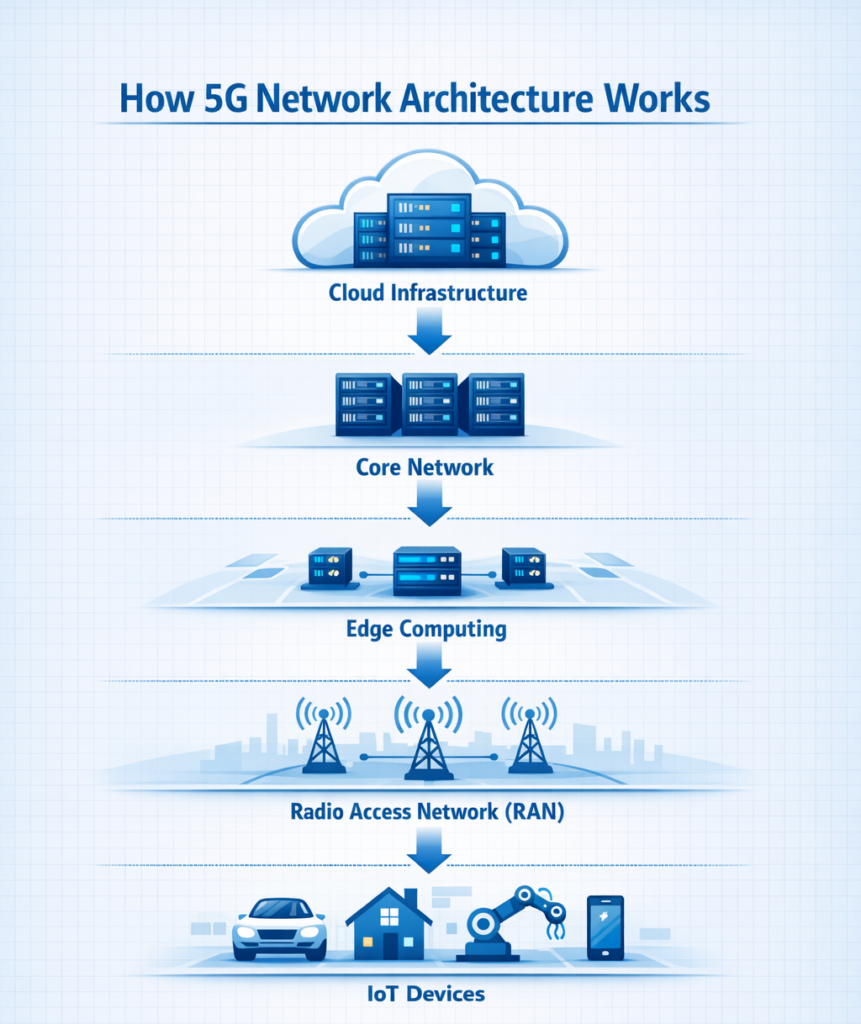
Decentralization Increases Complexity
Unlike centralized 4G systems, 5G architecture distributes functions across cloud and edge environments. Therefore, cybersecurity teams must secure:
- Core network
- Radio Access Network (RAN)
- Edge servers
- Virtualized infrastructure
- API integrations
This complexity requires automated monitoring and behavioral analytics.
New Cyber Threats Emerging in 5G Networks
1. IoT Botnet Expansion
Because 5G supports massive IoT connectivity, botnets can grow exponentially. In fact, compromised IoT devices can launch large-scale DDoS attacks.
Platforms like BotDef analyze malicious bot activity patterns and help mitigate automated threats.
2. Network Slice Exploitation
If attackers compromise one network slice, lateral movement may occur. Therefore, strict slice isolation policies are essential.
3. Edge Node Breaches
Edge computing improves performance. However, decentralized nodes may lack uniform security enforcement. As a result, attackers may target edge servers.
4. API Vulnerabilities
5G relies heavily on APIs. If APIs remain unsecured, attackers can exploit authentication weaknesses.
How 5G Can Improve Cybersecurity
Although risks increase, 5G also enhances security when properly implemented.
1. Enhanced Encryption Standards
5G includes stronger encryption protocols than 4G. Therefore, data interception becomes significantly harder.
2. AI-Driven Threat Detection
Because 5G networks generate massive data streams, AI-powered analytics become more effective.
Modern cybersecurity platforms use:
- Behavioral anomaly detection
- Real-time traffic analysis
- Predictive threat modeling
For example, AI-based predictive security models discussed in BotDef’s research explain how AI prevents attacks before execution.
3. Zero Trust Architecture
Zero Trust becomes essential in 5G ecosystems. Instead of trusting devices automatically, every access request must be verified.
🔎 “In a 5G world, trust is earned continuously — not assumed.”
🌐 5G and IoT Security – A Critical Intersection
The role of 5G in cybersecurity is particularly important in IoT environments.
Industrial IoT Risks
Manufacturing plants connected through 5G may face:
- Ransomware attacks
- Industrial espionage
- Data manipulation
Therefore, endpoint security and segmentation become mandatory.
AI + 5G = Predictive Cyber Defense
One of the rare but powerful advantages of 5G is predictive defense capability.
Because 5G reduces latency, AI engines can:
- Detect threats faster
- Respond instantly
- Block malicious packets before execution
This shift transforms cybersecurity from reactive to proactive.
Enterprise Strategy for Securing 5G
Step 1 – Conduct 5G Risk Assessment
Evaluate infrastructure vulnerabilities before deployment.
Step 2 – Implement Network Segmentation
Use micro-segmentation to isolate sensitive systems.
Step 3 – Deploy AI-Based Monitoring
Automated threat detection reduces human error.
Step 4 – Adopt Zero Trust
Verify identity continuously.
Step 5 – Secure Supply Chain
Ensure vendors follow security compliance standards.
The Future: Is 5G Safer?
The answer depends on implementation.
If organizations:
- Invest in AI-based security
- Enforce Zero Trust
- Protect APIs
- Monitor IoT devices
Then 5G can be both faster and safer.
However, without proper cybersecurity architecture, 5G could amplify cyber threats dramatically.
Conclusion
The role of 5G in cybersecurity is complex yet transformative. While 5G dramatically increases speed and connectivity, it also expands vulnerability surfaces. Therefore, security must evolve simultaneously.
Ultimately, 5G is not inherently unsafe. Instead, its safety depends on how organizations deploy and secure it.
🚀 “Technology advances. Security must advance faster.”







