In today’s digital world, staying secure isn’t just an option—it’s a necessity. As cyber threats continue to evolve, businesses and individuals are rapidly adopting smarter authentication systems. One of the most transformative approaches is biometric security, which relies on unique human characteristics instead of traditional passwords.
If you’re exploring advanced security solutions or keeping up with modern cybersecurity trends, platforms like BotDef’s security insights hub provide valuable updates on emerging technologies and best practices.
This blog dives deep into Biometric Security: Fingerprints vs. Facial Recognition vs. Voice ID, helping you understand how each method works, their advantages, limitations, and where they fit in real-world applications.
What is Biometric Security?
Biometric security refers to authentication systems that verify identity using unique biological or behavioral traits. Unlike passwords, biometrics are difficult to replicate, making them a powerful defense against unauthorized access.
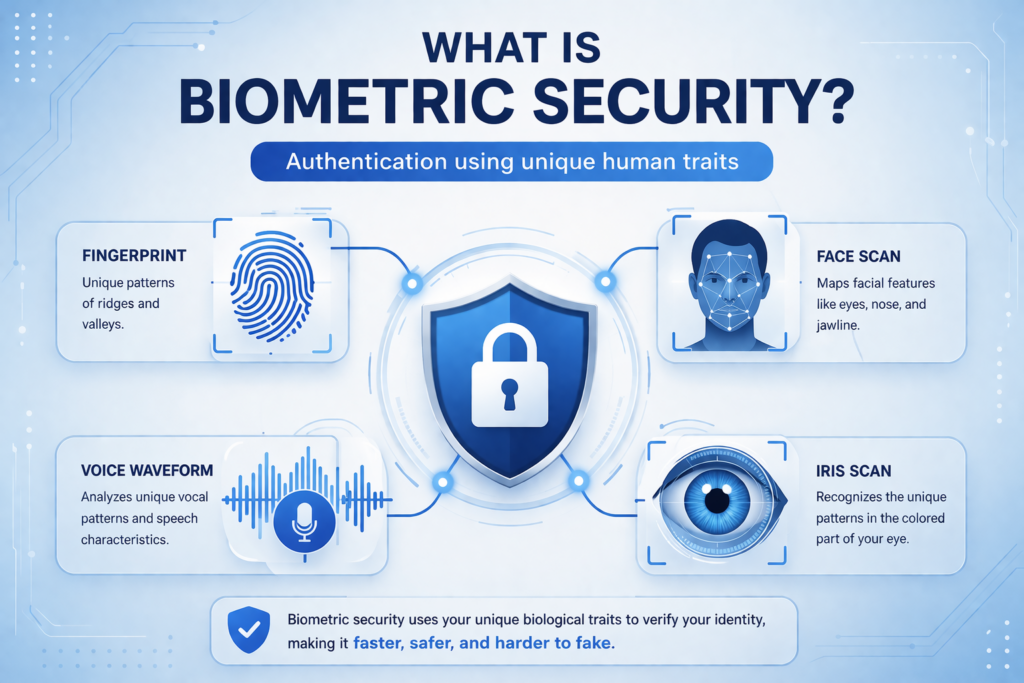
Common Types of Biometric Authentication
- Fingerprint recognition
- Facial recognition
- Voice identification
- Iris scanning
- Behavioral biometrics (typing patterns, gait)
Among these, fingerprints, facial recognition, and voice ID are the most widely used due to their convenience and scalability.
Why Biometric Security is Gaining Popularity
Before comparing technologies, it’s important to understand why biometric security is becoming the standard.
Key Benefits
- Enhanced Security – Harder to duplicate than passwords
- User Convenience – No need to remember credentials
- Faster Authentication – Instant access with minimal effort
- Reduced Fraud Risk – Limits identity theft and phishing attacks
Moreover, according to the National Institute of Standards and Technology (NIST), biometric systems significantly improve identity assurance when implemented correctly.
Fingerprint Recognition: The Classic Standard
Fingerprint authentication has been around for decades and remains one of the most trusted biometric methods.

How It Works
Fingerprint systems scan the unique patterns of ridges and valleys on a user’s finger. These patterns are converted into digital templates and stored securely.
Advantages of Fingerprint Authentication
- High Accuracy – Proven reliability over time
- Fast Processing – Instant unlocking on devices
- Cost-Effective – Widely available and affordable
- Offline Capability – Doesn’t always require internet
Limitations
- Physical Wear – Cuts or dirt can affect accuracy
- Spoofing Risks – Advanced fake fingerprints can sometimes bypass systems
- Limited Remote Use – Requires physical presence
Real-World Use Cases
- Smartphones and laptops
- Office access systems
- Banking authentication
Even today, fingerprint recognition remains a foundational component in many biometric security systems, especially where reliability is critical.
Facial Recognition: The AI-Driven Approach
Facial recognition has seen rapid growth thanks to advancements in artificial intelligence and computer vision.
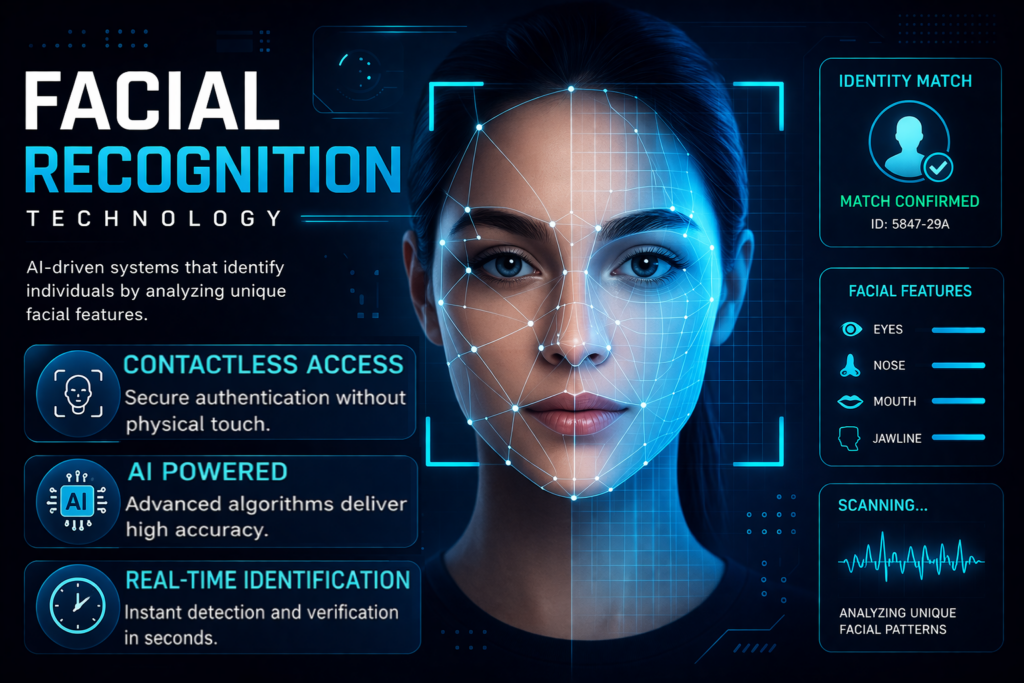
How Facial Recognition Works
This system maps facial features such as:
- Distance between eyes
- Jawline structure
- Nose shape
- Skin texture
It then compares this data with stored templates to verify identity.
Advantages of Facial Recognition
- Contactless Authentication – Ideal for hygiene-conscious environments
- Scalable – Can identify multiple individuals in real time
- User-Friendly – No physical interaction required
- Remote Verification – Works across devices and locations
Limitations
- Privacy Concerns – Raises ethical and legal issues
- Lighting Sensitivity – Performance may vary in poor lighting
- False Positives – Risk of misidentification in some cases
Use Cases
- Airport security systems
- Smartphone face unlock
- Surveillance and law enforcement
Interestingly, modern systems are integrating facial recognition with liveness detection to prevent spoofing attacks, making it more secure than earlier versions.
If you’re exploring how AI enhances cybersecurity frameworks, you can also refer to BotDef’s AI-driven threat detection resources, which explain how machine learning improves biometric accuracy.
Voice ID: The Emerging Contender
Voice identification is gaining traction, especially in remote authentication scenarios.

How Voice ID Works
Voice ID analyzes:
- Tone and pitch
- Speech patterns
- Accent and pronunciation
- Vocal tract characteristics
These features create a unique voiceprint for each user.
Advantages of Voice Authentication
- Hands-Free Access – Ideal for mobile and IoT devices
- Remote Authentication – Works over calls or virtual assistants
- Accessible – Useful for visually impaired users
Limitations
- Background Noise Sensitivity
- Voice Changes – Illness or aging can affect accuracy
- Replay Attacks – Recorded voices can sometimes trick systems
Use Cases
- Customer service authentication
- Smart home devices
- Banking via phone systems
Despite its challenges, voice ID is becoming a key part of multi-factor biometric security systems.
Fingerprints vs. Facial Recognition vs. Voice ID: A Detailed Comparison
To better understand Biometric Security: Fingerprints vs. Facial Recognition vs. Voice ID, let’s compare them across critical factors.
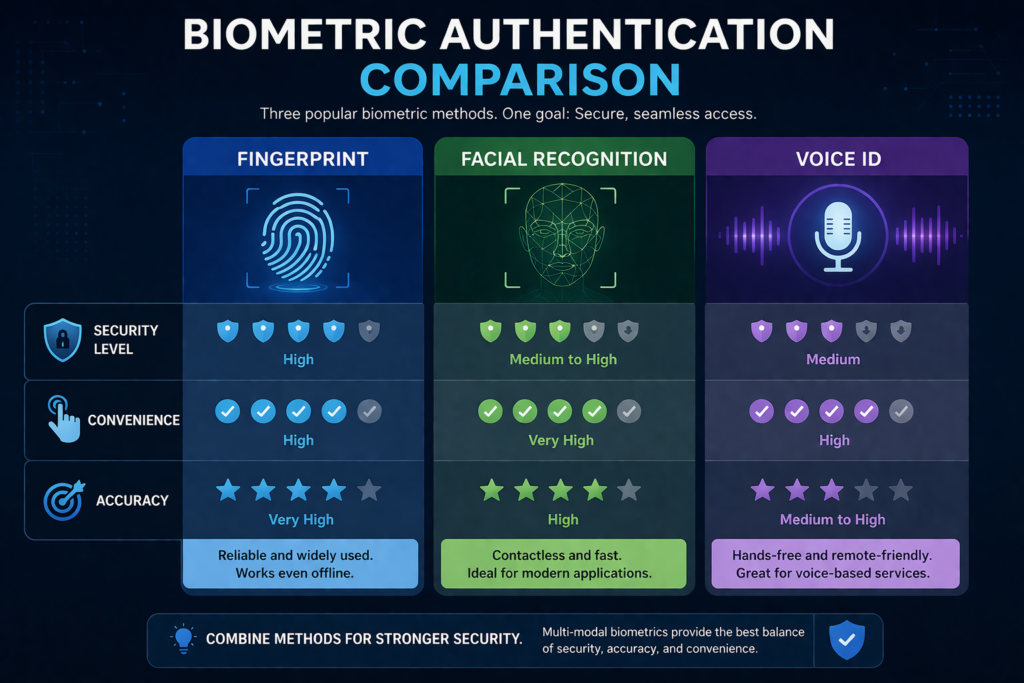
1. Security Level
- Fingerprint – High (but vulnerable to physical spoofing)
- Facial Recognition – Medium to High (improving with AI)
- Voice ID – Medium (susceptible to replay attacks)
2. Convenience
- Fingerprint – Requires touch
- Facial Recognition – Fully contactless
- Voice ID – Hands-free and remote
3. Accuracy
- Fingerprint – Very high
- Facial Recognition – High (with good lighting and AI models)
- Voice ID – Moderate
4. Cost and Implementation
- Fingerprint – Affordable and widely available
- Facial Recognition – Moderate to high cost
- Voice ID – Cost-effective for remote systems
5. Best Use Cases
- Fingerprint – Personal devices, secure access
- Facial Recognition – Surveillance, airports
- Voice ID – Call centers, smart assistants
The Rise of Multi-Modal Biometric Security
Instead of relying on a single method, organizations are increasingly adopting multi-modal biometric security.
What is Multi-Modal Biometrics?
It combines two or more biometric methods, such as:
- Fingerprint + Facial Recognition
- Facial Recognition + Voice ID
- Fingerprint + PIN
Benefits
- Higher Security – Reduces chances of spoofing
- Better Accuracy – Combines strengths of multiple systems
- Improved User Experience – Flexible authentication options
For example, a banking app may use facial recognition for login and voice ID for transaction verification.
Security Risks and Ethical Considerations
While biometric security offers many advantages, it’s not without concerns.
Key Risks
- Data Breaches – Biometric data cannot be changed like passwords
- Surveillance Misuse – Facial recognition can be abused
- Bias in AI Models – Accuracy may vary across demographics
The European Union Agency for Cybersecurity (ENISA) emphasizes the importance of secure storage and ethical implementation of biometric systems.
Best Practices for Implementing Biometric Security
If you’re planning to adopt biometric authentication, consider the following:
1. Use Encryption
Always store biometric data in encrypted formats to prevent unauthorized access.
2. Enable Multi-Factor Authentication
Combine biometrics with:
- OTPs
- PINs
- Security tokens
3. Regular System Updates
Keep biometric systems updated to defend against evolving threats.
4. Ensure User Consent
Transparency is critical when collecting biometric data.
5. Monitor and Audit Systems
Continuous monitoring helps detect anomalies early.
To explore practical implementation strategies and security frameworks, you can refer to BotDef’s advanced cybersecurity solutions, which highlight modern defense mechanisms against identity-based threats.
Future of Biometric Security
The future of Biometric Security: Fingerprints vs. Facial Recognition vs. Voice ID lies in innovation and integration.
Emerging Trends
- Behavioral Biometrics (typing speed, gestures)
- AI-Powered Fraud Detection
- Decentralized Identity Systems
- Biometric Authentication in Blockchain
As technology evolves, biometric systems will become more accurate, secure, and widely adopted across industries.
Conclusion
Biometric Security: Fingerprints vs. Facial Recognition vs. Voice ID is no longer a theoretical discussion—it’s a practical necessity in modern cybersecurity.
Each method has its strengths:
- Fingerprints offer reliability and accuracy
- Facial recognition provides convenience and scalability
- Voice ID enables remote and hands-free authentication
However, no single solution is perfect. Therefore, the most effective approach is often a combination of multiple biometric systems.
As organizations continue to prioritize digital security, adopting advanced biometric strategies will be crucial. By staying informed and implementing best practices, businesses can significantly reduce risks while enhancing user experience.