In today’s fast-paced digital landscape, businesses are increasingly relying on automation to improve efficiency and reduce operational costs. Among the most transformative technologies is Robotic Process Automation (RPA)—a solution that enables organizations to automate repetitive, rule-based tasks with precision and speed. However, as adoption grows, so do the risks associated with it. Understanding Robotic Process Automation (RPA) and its security challenges is now critical for businesses aiming to scale securely.
At the same time, platforms like BotDef’s security insights hub emphasize that automation without strong security frameworks can expose organizations to serious threats. This blog explores how RPA works, the security risks it introduces, and practical strategies to mitigate those risks effectively.
What is Robotic Process Automation (RPA)?
Robotic Process Automation refers to the use of software bots that mimic human actions to perform repetitive tasks. These bots interact with applications, process data, trigger responses, and communicate with systems—just like a human employee would.
Key Features of RPA
- Rule-based task automation
- Integration with multiple systems without deep coding
- Increased operational efficiency
- Reduced human error
- Scalability across departments
RPA is widely used in industries such as finance, healthcare, customer service, and IT operations. For example, bots can handle invoice processing, data entry, compliance reporting, and customer onboarding.
However, while RPA boosts productivity, it also introduces new security complexities.
Why Security is Critical in RPA
When organizations deploy RPA, they often grant bots access to sensitive systems and data. These bots can perform high-privilege actions, making them attractive targets for cyber threats.
Moreover, unlike human users, bots operate continuously and at scale. If compromised, they can cause widespread damage in a short time.
Key Reasons Security Matters in RPA
- Bots often have elevated access privileges
- They handle sensitive business and customer data
- Misconfigurations can lead to data leaks or unauthorized actions
- Lack of monitoring increases risk exposure
According to global cybersecurity guidelines from sources like the National Institute of Standards and Technology (NIST), automation systems must follow strict security frameworks to prevent exploitation.
Common Security Challenges in RPA
Understanding the core risks is the first step toward building a secure RPA ecosystem.
1. Credential Management Risks
RPA bots require credentials to access systems. However, storing these credentials improperly can lead to serious vulnerabilities.
Key Issues:
- Hardcoded credentials in scripts
- Weak password policies
- Lack of encryption
If attackers gain access to these credentials, they can control bots and exploit systems.
2. Lack of Proper Access Control
Bots often have more permissions than necessary, violating the principle of least privilege.
Risks Include:
- Unauthorized data access
- System manipulation
- Increased insider threat exposure
Organizations must ensure that bots only have access to what is strictly required.
3. Inadequate Monitoring and Logging
Many organizations fail to monitor bot activities effectively.
Consequences:
- Delayed detection of suspicious activity
- Difficulty in forensic investigations
- Increased compliance risks
Without proper logging, tracking malicious actions becomes nearly impossible.
4. Vulnerabilities in Bot Development
RPA scripts are often developed quickly to meet business demands. As a result, security best practices may be overlooked.
Common Issues:
- Lack of input validation
- Poor exception handling
- Unsecured APIs
This creates opportunities for attackers to exploit vulnerabilities.
5. Data Privacy and Compliance Risks
RPA bots frequently process sensitive personal and financial data. Improper handling can lead to compliance violations.
Examples:
- Exposure of customer data
- Violation of GDPR or other regulations
- Data leakage during processing
This not only affects reputation but also leads to legal penalties.
6. Bot Hijacking and Manipulation
If attackers gain control of bots, they can execute malicious operations at scale.
Potential Impact:
- Financial fraud
- Data corruption
- System downtime
Because bots operate faster than humans, damage can escalate quickly.
Real-World Example of RPA Security Risk

Consider a financial organization that deploys RPA bots for transaction processing. If these bots use shared credentials and lack monitoring, an attacker could:
- Gain access to the bot system
- Modify transaction rules
- Execute unauthorized transfers
This scenario highlights why Robotic Process Automation (RPA) and its security challenges must be addressed proactively.
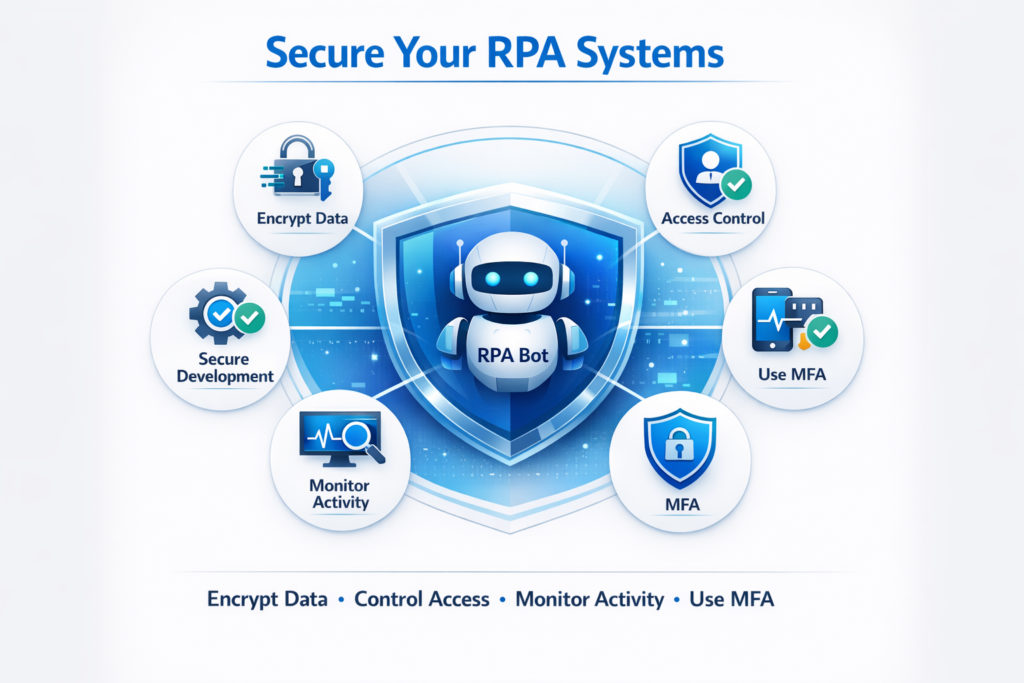
Best Practices to Secure RPA Systems
To mitigate risks, organizations must implement strong security frameworks alongside automation.
1. Implement Strong Credential Management
- Use secure credential vaults
- Avoid hardcoding sensitive data
- Enable multi-factor authentication (MFA)
2. Apply the Principle of Least Privilege
- Restrict bot access to necessary systems only
- Regularly review permissions
- Separate duties across bots
3. Enable Continuous Monitoring
- Track bot activities in real time
- Use security information and event management (SIEM) tools
- Set alerts for unusual behavior
For deeper insights into monitoring strategies, you can explore BotDef’s advanced threat detection resources, which highlight modern approaches to securing automated workflows.
4. Secure the Development Lifecycle
- Follow secure coding practices
- Conduct regular code reviews
- Perform vulnerability assessments
Integrating security into development ensures fewer risks in production.
5. Encrypt Sensitive Data
- Encrypt data at rest and in transit
- Use secure communication protocols
- Protect API integrations
6. Conduct Regular Audits
- Perform compliance checks
- Review logs and system activity
- Identify and fix vulnerabilities
7. Use Role-Based Access Control (RBAC)
- Assign roles based on responsibilities
- Limit administrative privileges
- Monitor access changes
Emerging Trends in RPA Security
As RPA evolves, so do the strategies to secure it.
AI-Driven Security Monitoring
Artificial intelligence is being used to detect anomalies in bot behavior, enabling faster threat detection.
Zero Trust Architecture
Organizations are adopting zero trust models where no entity is trusted by default—even bots.
Integration with Cybersecurity Platforms
Modern RPA solutions are integrating with advanced security platforms to provide end-to-end protection.
You can also explore global cybersecurity perspectives from resources like the Cybersecurity & Infrastructure Security Agency (CISA) to understand how automation security is shaping the future.
Challenges in Balancing Automation and Security
While security is essential, overcomplicating it can reduce the efficiency of RPA systems.
Key Challenges:
- Maintaining performance while enforcing security
- Managing complex bot ecosystems
- Ensuring compliance across regions
Therefore, organizations must strike a balance between automation speed and security control.
How Businesses Can Build a Secure RPA Strategy
A successful RPA strategy integrates security from the beginning rather than treating it as an afterthought.
Steps to Build a Secure Framework:
- Assess Risks Early
Identify potential vulnerabilities before deployment - Define Security Policies
Establish clear guidelines for bot usage - Train Teams
Educate developers and IT teams on security best practices - Adopt Security Tools
Use advanced monitoring and threat detection systems - Continuously Improve
Regularly update systems based on emerging threats
Additionally, leveraging trusted platforms like BotDef’s cybersecurity solutions can help organizations stay ahead of evolving risks while maintaining operational efficiency.
Conclusion
Robotic Process Automation is revolutionizing how businesses operate. It offers speed, accuracy, and scalability that traditional processes simply cannot match. However, with these benefits come significant risks.
Understanding Robotic Process Automation (RPA) and its security challenges is essential for any organization adopting automation. From credential management to bot monitoring, every aspect of RPA must be secured to prevent potential threats.
By implementing strong security practices, leveraging modern tools, and staying informed through platforms like BotDef, businesses can unlock the full potential of RPA without compromising safety.
In the end, automation should not just be smart—it should be secure.